Expert Verified, Online, Free.

An organization is referencing NIST best practices for BCP creation while reviewing current internal organizational processes for mission-essential items.
Which of the following phases establishes the identification and prioritization of critical systems and functions?
Correct Answer:
A
🗳️
Reference:
https://itsm.ucsf.edu/business-impact-analysis-bia-0
An organization is preparing to migrate its production environment systems from an on-premises environment to a cloud service. The lead security architect is concerned that the organization's current methods for addressing risk may not be possible in the cloud environment.
Which of the following BEST describes the reason why traditional methods of addressing risk may not be possible in the cloud?
Correct Answer:
C
🗳️
Reference:
https://arxiv.org/ftp/arxiv/papers/1303/1303.4814.pdf
A company created an external application for its customers. A security researcher now reports that the application has a serious LDAP injection vulnerability that could be leveraged to bypass authentication and authorization.
Which of the following actions would BEST resolve the issue? (Choose two.)
Correct Answer:
EF
🗳️
In preparation for the holiday season, a company redesigned the system that manages retail sales and moved it to a cloud service provider. The new infrastructure did not meet the company's availability requirements. During a postmortem analysis, the following issues were highlighted:
1. International users reported latency when images on the web page were initially loading.
2. During times of report processing, users reported issues with inventory when attempting to place orders.
3. Despite the fact that ten new API servers were added, the load across servers was heavy at peak times.
Which of the following infrastructure design changes would be BEST for the organization to implement to avoid these issues in the future?
Correct Answer:
A
🗳️
During a remodel, a company's computer equipment was moved to a secure storage room with cameras positioned on both sides of the door. The door is locked using a card reader issued by the security team, and only the security team and department managers have access to the room. The company wants to be able to identify any unauthorized individuals who enter the storage room by following an authorized employee.
Which of the following processes would BEST satisfy this requirement?
Correct Answer:
A
🗳️
Reference:
https://www.getkisi.com/access-control
A company is preparing to deploy a global service.
Which of the following must the company do to ensure GDPR compliance? (Choose two.)
Correct Answer:
AC
🗳️
Reference:
https://gdpr.eu/compliance-checklist-us-companies/
A SOC analyst is reviewing malicious activity on an external, exposed web server. During the investigation, the analyst determines specific traffic is not being logged, and there is no visibility from the WAF for the web application.
Which of the following is the MOST likely cause?
Correct Answer:
B
🗳️
Reference:
https://aws.amazon.com/premiumsupport/knowledge-center/waf-block-http-requests-no-user-agent/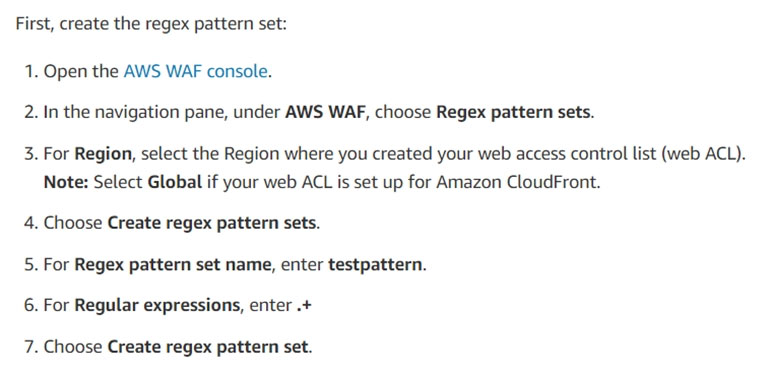
A security analyst is reviewing the following output: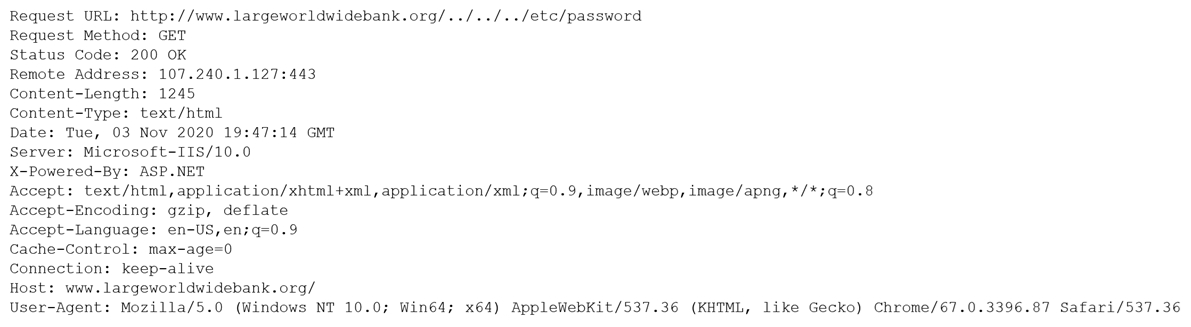
Which of the following would BEST mitigate this type of attack?
Correct Answer:
B
🗳️
Which of the following terms refers to the delivery of encryption keys to a CASB or a third-party entity?
Correct Answer:
D
🗳️
Reference:
https://www.open.edu/openlearn/ocw/mod/oucontent/view.php?id=48322§ion=1.3
An organization is implementing a new identity and access management architecture with the following objectives:
✑ Supporting MFA against on-premises infrastructure
✑ Improving the user experience by integrating with SaaS applications
✑ Applying risk-based policies based on location
✑ Performing just-in-time provisioning
Which of the following authentication protocols should the organization implement to support these requirements?
Correct Answer:
D
🗳️
Reference:
https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/migrate-application-authentication-to-azure-active-directory