

SIMULATION -
You are a penetration tester running port scans on a server.
INSTRUCTIONS -
Part 1: Given the output, construct the command that was used to generate this output from the available options.
Part 2: Once the command is appropriately constructed, use the given output to identify the potential attack vectors that should be investigated further.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Part 1 -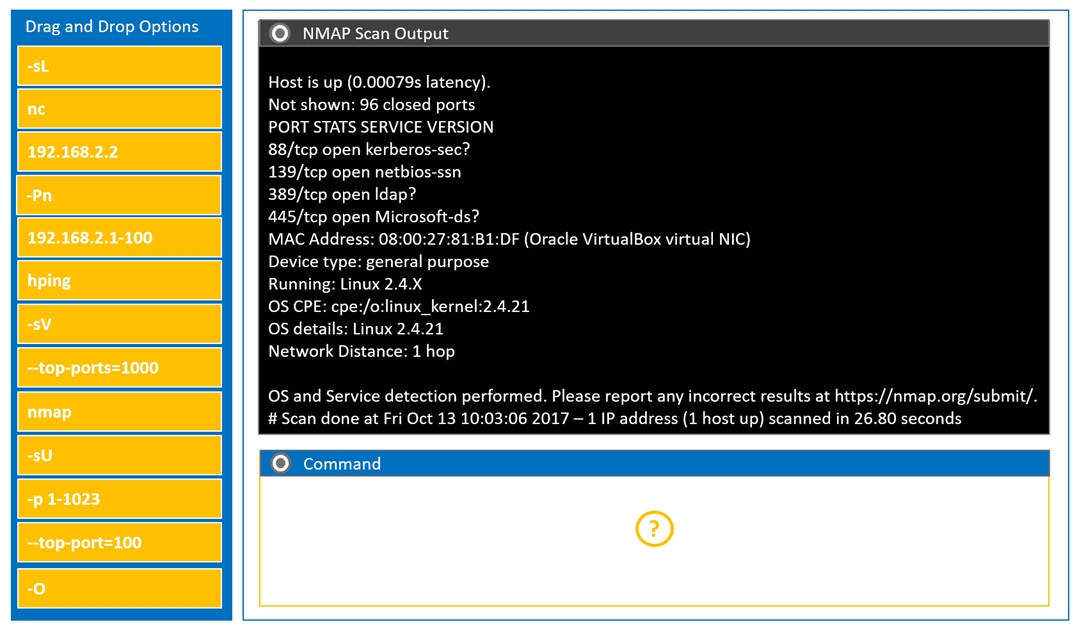
Part 2 -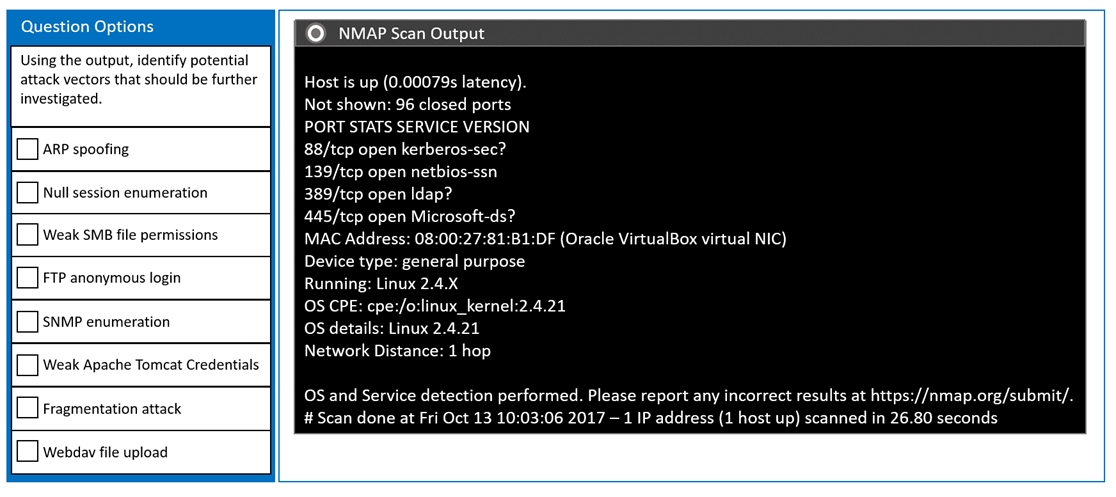
ryanzou
Highly Voted 2 years, 9 months agoAnarckii
Highly Voted 2 years agoeuca2023
Most Recent 2 months, 3 weeks agoJblak
3 months, 3 weeks agojont
1 month, 1 week agoDtones2423
4 months, 1 week agoFart2023
9 months agopinderanttal
6 months agoFart2023
9 months ago10c9c83
1 month, 1 week agoHunterxSeb
10 months, 4 weeks agoElDirec
1 year, 5 months agoLiveLaughToasterBath
1 year, 5 months ago[Removed]
1 year, 6 months agoDRVision
1 year, 7 months agoMysterClyde
2 years agosurfuganda
1 year, 3 months agotaylorhung
1 year, 7 months agoTheSkyMan
2 years, 2 months agocy_analyst
2 years, 3 months ago[Removed]
2 years, 3 months agoKingIT_ENG
2 years, 3 months agoFrog_Man
2 years, 3 months ago[Removed]
2 years, 3 months ago2Fish
2 years, 4 months ago2Fish
2 years, 4 months ago[Removed]
2 years, 4 months agouser82
1 year, 4 months ago