

DRAG DROP -
Drag and drop the cloud deployment model to the associated use-case scenario. Options may be used only once or not at all.
Select and Place: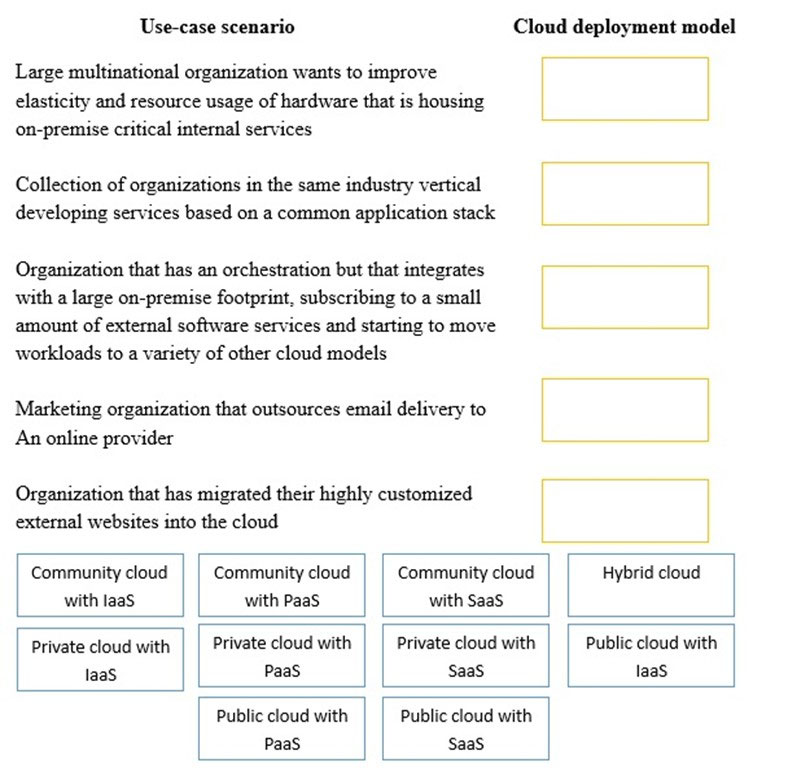
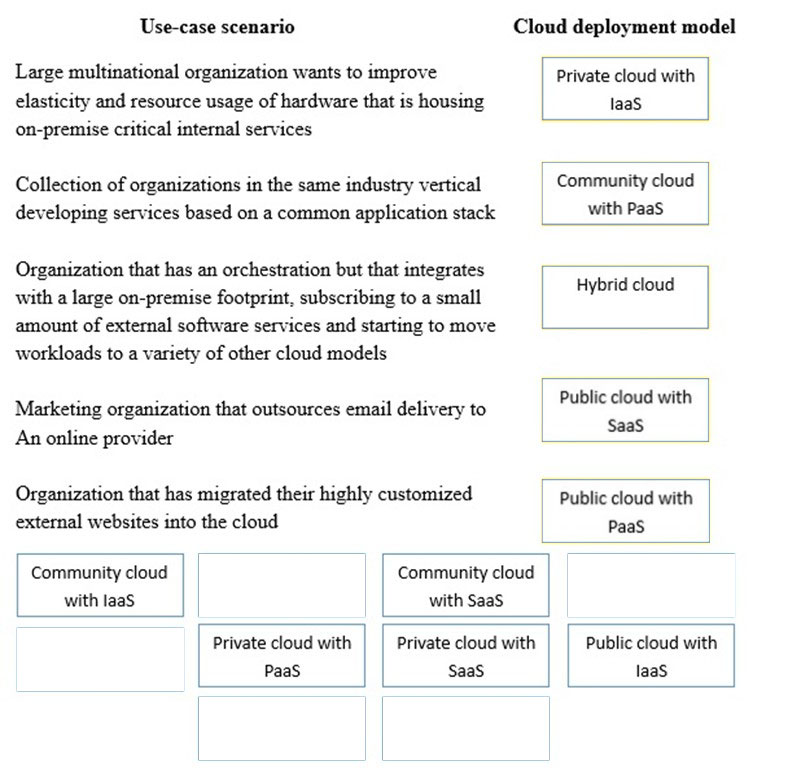
Correct Answer:
DRAG DROP -
A security consultant is considering authentication options for a financial institution. The following authentication options are available. Drag and drop the security mechanism to the appropriate use case. Options may be used once.
Select and Place: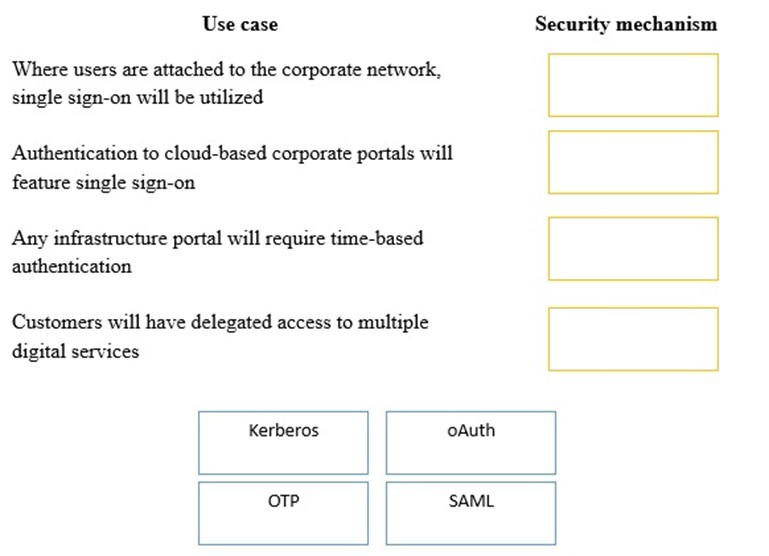
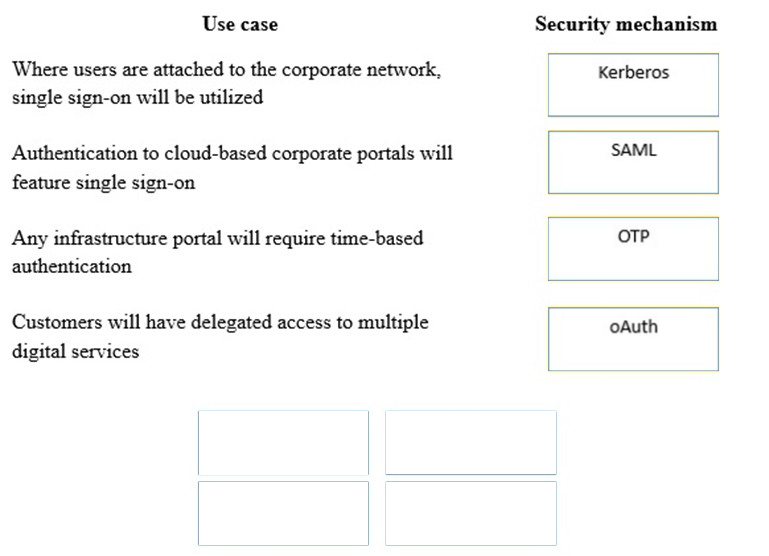
Correct Answer:
A company's Chief Operating Officer (COO) is concerned about the potential for competitors to infer proprietary information gathered from employees' social media accounts.
Which of the following methods should the company use to gauge its own social media threat level without targeting individual employees?
Correct Answer:
A
🗳️
DRAG DROP -
A security administrator must configure the database server shown below to comply with the four requirements listed. Drag and drop the appropriate ACL that should be configured on the database server to its corresponding requirement. Answer options may be used once or not at all.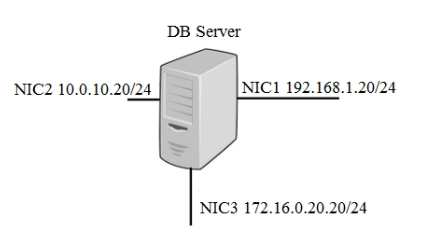
Select and Place: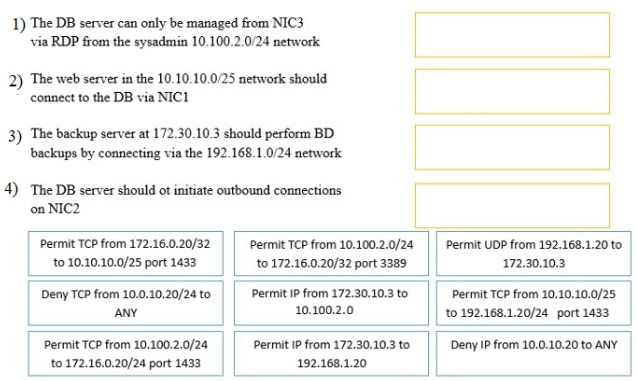
Correct Answer:
A security administrator is hardening a TrustedSolaris server that processes sensitive data. The data owner has established the following security requirements:
✑ The data is for internal consumption only and shall not be distributed to outside individuals
✑ The systems administrator should not have access to the data processed by the server
✑ The integrity of the kernel image is maintained
Which of the following host-based security controls BEST enforce the data owner's requirements? (Choose three.)
Correct Answer:
CEF
🗳️
An SQL database is no longer accessible online due to a recent security breach. An investigation reveals that unauthorized access to the database was possible due to an SQL injection vulnerability. To prevent this type of breach in the future, which of the following security controls should be put in place before bringing the database back online? (Choose two.)
Correct Answer:
CF
🗳️
A company has entered into a business agreement with a business partner for managed human resources services. The Chief Information Security Officer (CISO) has been asked to provide documentation that is required to set up a business-to-business VPN between the two organizations. Which of the following is required in this scenario?
Correct Answer:
A
🗳️
Given the following output from a local PC: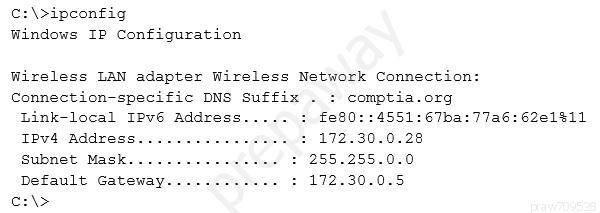
Which of the following ACLs on a stateful host-based firewall would allow the PC to serve an intranet website?
Correct Answer:
B
🗳️
A penetration tester has been contracted to conduct a physical assessment of a site. Which of the following is the MOST plausible method of social engineering to be conducted during this engagement?
Correct Answer:
A
🗳️
A penetration tester is conducting an assessment on Comptia.org and runs the following command from a coffee shop while connected to the public Internet: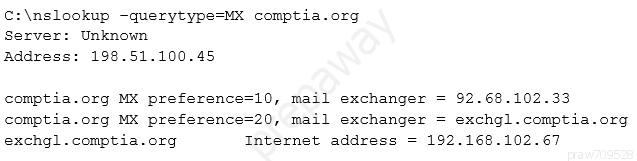
Which of the following should the penetration tester conclude about the command output?
Correct Answer:
B
🗳️