
Expert Verified, Online, Free.

Adam, a malicious hacker has successfully gained unauthorized access to the Linux system of
Umbrella Inc. Web server of the company runs on Apache. He has downloaded sensitive documents and database files from the computer. After performing these malicious tasks, Adam finally runs the following command on the Linux command box before disconnecting. for (( i = 0;i<11;i++ )); do dd if=/dev/random of=/dev/hda && dd if=/dev/zero of=/dev/hda done
Which of the following actions does Adam want to perform by the above command?
Correct Answer:
C
🗳️
Adam works as a Computer Hacking Forensic Investigator for a garment company in the United States. A project has been assigned to him to investigate a case of a disloyal employee who is suspected of stealing design of the garments, which belongs to the company and selling those garments of the same design under different brand name. Adam investigated that the company does not have any policy related to the copy of design of the garments. He also investigated that the trademark under which the employee is selling the garments is almost identical to the original trademark of the company. On the grounds of which of the following laws can the employee be prosecuted?
Correct Answer:
A
🗳️
You work as a Network Administrator for Perfect Solutions Inc. You install Windows 98 on a computer. By default, which of the following folders does Windows 98 setup use to keep the registry tools?
Correct Answer:
B
🗳️
Which of the following tools can be used to perform tasks such as Windows password cracking, Windows enumeration, and VoIP session sniffing?
Correct Answer:
D
🗳️
Which of the following type of file systems is not supported by Linux kernel?
Correct Answer:
D
🗳️
Which of the following modules of OS X kernel (XNU) provides the primary system program interface?
Correct Answer:
A
🗳️
You work as a Network Administrator for Blue Bell Inc. You want to install Windows XP Professional on your computer, which already has Windows Me installed.
You want to configure your computer to dual boot between Windows Me and Windows XP Professional. You have a single 40GB hard disk.
Which of the following file systems will you choose to dual-boot between the two operating systems?
Correct Answer:
B
🗳️
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He receives the following e- mail: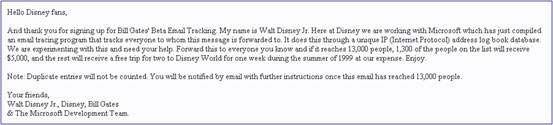
The e-mail that John has received is an example of __________.
Correct Answer:
D
🗳️
Which of the following Acts enacted in United States allows the FBI to issue National Security Letters (NSLs) to Internet service providers (ISPs) ordering them to disclose records about their customers?
Correct Answer:
D
🗳️
TCP FIN scanning is a type of stealth scanning through which the attacker sends a FIN packet to the target port. If the port is closed, the victim assumes that this packet was sent mistakenly by the attacker and sends the RST packet to the attacker. If the port is open, the FIN packet will be ignored and the port will drop the packet. Which of the following operating systems can be easily identified with the help of TCP FIN scanning?
Correct Answer:
D
🗳️