
Expert Verified, Online, Free.

A user suspects someone has been accessing a home network without permission by spoofing the MAC address of an authorized system. While attempting to determine if an authorized user is logged into the home network, the user reviews the wireless router, which shows the following table for systems that are currently on the home network.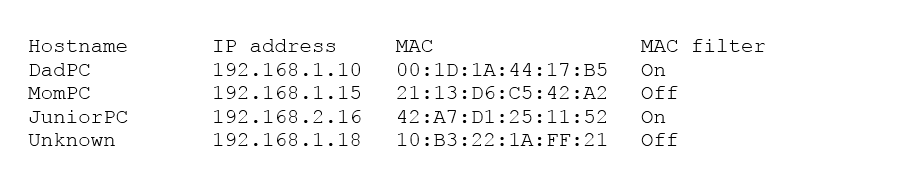
Which of the following should be the NEXT step to determine if there is an unauthorized user on the network?
rahimtolba
Highly Voted 4 years, 4 months agoMelvinJohn
Highly Voted 4 years agoMortG7
Most Recent 3 years, 2 months agowho__cares123456789___
3 years, 3 months agowho__cares123456789___
3 years, 3 months agowho__cares123456789___
3 years, 3 months agoHuh
3 years, 3 months agoHanzero
3 years, 7 months agomaxjak
3 years, 8 months agorameces
3 years, 8 months agoTedaroo
3 years, 5 months agokentasmith
3 years, 8 months agokentasmith
3 years, 8 months agoHot_156
3 years, 11 months agorenegade_xt
3 years, 11 months agoDante_Dan
4 years, 1 month agomacshild
4 years, 4 months agoredondo310
4 years, 4 months agoAsmin
4 years, 7 months agoKakster
2 years, 9 months agoBasem
4 years, 8 months ago